Key Insights
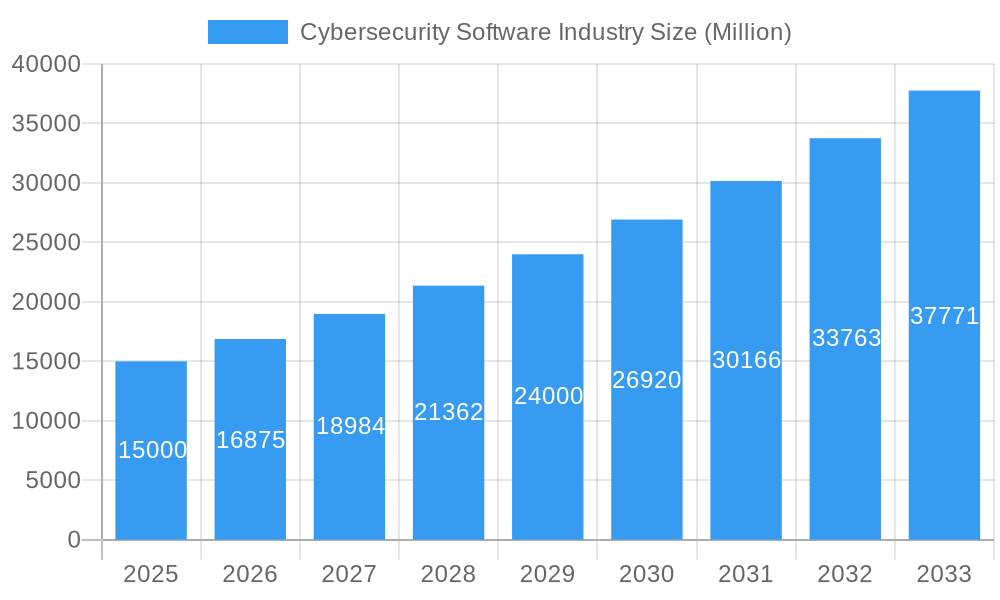
The global cybersecurity software market, currently valued at approximately $XX million in 2025 (assuming a logical extrapolation based on the provided CAGR of 12.50% and a 2019-2024 historical period), is experiencing robust growth, projected to reach a significant size by 2033. This expansion is fueled by several key drivers, including the increasing prevalence of cyberattacks targeting businesses and individuals, the growing adoption of cloud computing and IoT devices expanding attack surfaces, and the stringent regulatory landscape demanding robust cybersecurity measures. The market is segmented by offering (software and services), deployment (on-premises and cloud – with cloud experiencing faster growth), and end-user (BFSI, healthcare, manufacturing, government & defense, IT & telecommunications being major segments). The strong preference for cloud-based solutions reflects the inherent scalability, accessibility, and cost-effectiveness they offer compared to on-premises deployments. Furthermore, the increasing sophistication of cyber threats necessitates continuous investment in advanced security technologies, fostering market growth. While data breaches and associated costs represent a significant restraint, the overall market outlook remains positive due to ongoing technological advancements and rising awareness regarding cybersecurity risks.
Cybersecurity Software Industry Market Size (In Billion)

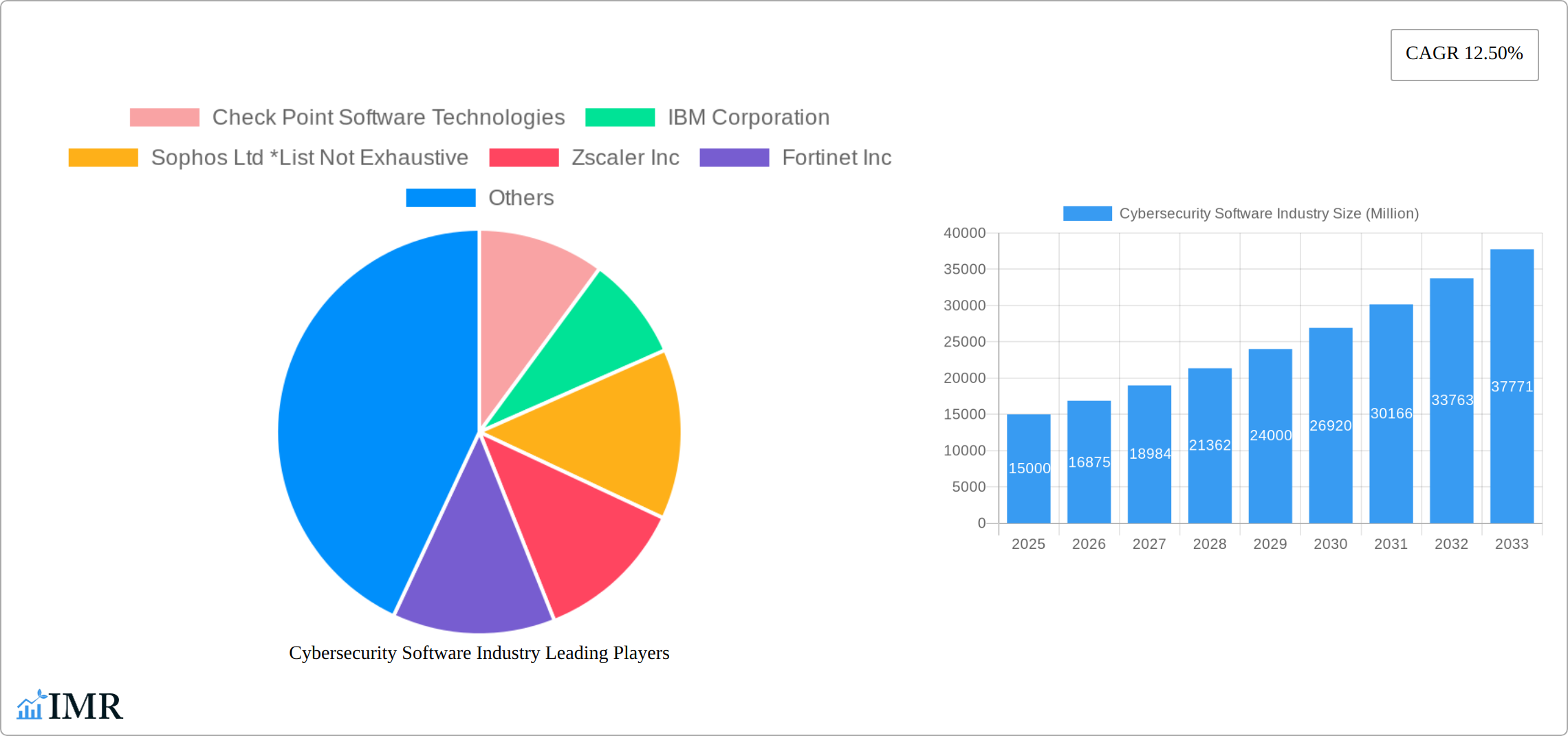
The competitive landscape is characterized by both established players (like Check Point, IBM, Sophos, Zscaler, Fortinet, F5 Networks, Cisco, Broadcom, Microsoft, Proofpoint, Mandiant, CyberArk, and Palo Alto Networks) and emerging innovative companies. The market's regional distribution sees North America holding a substantial market share initially, driven by robust technological infrastructure and high cybersecurity awareness. However, regions like Asia-Pacific and Europe are expected to witness significant growth in the forecast period due to increasing digitalization and government initiatives promoting cybersecurity. The competitive intensity is high, with companies focusing on strategic partnerships, mergers and acquisitions, and product innovation to maintain their market positions. This dynamic interplay of market forces and technological advancements suggests a continuously evolving cybersecurity software landscape poised for sustained expansion in the coming years.
Cybersecurity Software Industry Company Market Share

Cybersecurity Software Industry Market Report: 2019-2033
This comprehensive report provides an in-depth analysis of the global Cybersecurity Software industry, covering market dynamics, growth trends, regional segmentation, product landscape, key players, and future outlook. The study period spans from 2019 to 2033, with 2025 serving as the base and estimated year. The report analyzes the parent market of Cybersecurity Software and delves into its child markets, offering granular insights for informed decision-making. The market size is presented in million units.
Cybersecurity Software Industry Market Dynamics & Structure
The global cybersecurity software market is a dynamic and rapidly evolving landscape, marked by a high degree of fragmentation. While numerous players contribute to the market's vibrancy, a select group of prominent vendors, including Check Point Software Technologies, IBM Corporation, and Sophos Ltd, maintain substantial market influence. The market exhibits moderate concentration, with ongoing consolidation driven by strategic mergers and acquisitions (M&A). A primary catalyst for market expansion is continuous technological innovation, particularly advancements in artificial intelligence (AI) and machine learning (ML) for threat detection and response. Furthermore, stringent regulatory frameworks such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) are profoundly shaping industry practices and compliance mandates. Competitive pressures are exacerbated by the availability of cost-effective open-source alternatives and the ever-increasing sophistication and adaptability of cyber threats.
- Market Concentration: The market exhibits moderate concentration, with the top 10 players projected to hold approximately 65% of the market share by 2025, indicating a trend towards larger entities dominating key segments.
- Technological Innovation: Key growth drivers include the widespread adoption of AI-powered threat detection and response systems, advanced endpoint protection solutions offering comprehensive device security, and robust cloud security solutions designed to safeguard data and applications in distributed environments.
- Regulatory Frameworks: Evolving regulations like GDPR, CCPA, and emerging regional data protection laws are compelling organizations to prioritize robust data security, privacy controls, and transparent compliance practices, driving demand for compliant software solutions.
- M&A Activity: Significant M&A activity is a defining characteristic of the market, fueling consolidation and the emergence of integrated security platforms. The volume of M&A deals averaged around 35 per year between 2019 and 2024, reflecting strategic moves to acquire innovative technologies and expand market reach.
- End-User Demographics: The Banking, Financial Services, and Insurance (BFSI), Healthcare, and Government & Defense sectors represent the largest and most critical end-user segments. These sectors are characterized by stringent regulatory requirements, the handling of highly sensitive data, and a constant threat of sophisticated attacks, necessitating advanced cybersecurity measures.
Cybersecurity Software Industry Growth Trends & Insights
The global cybersecurity software market experienced significant growth between 2019 and 2024, driven by increasing cyber threats, rising digitalization, and expanding cloud adoption. The market size reached xx million units in 2024, with a Compound Annual Growth Rate (CAGR) of xx% during this period. Market penetration varies significantly across regions and end-user sectors, with mature markets exhibiting slower growth compared to emerging economies. Technological disruptions such as the rise of IoT and 5G networks have presented new challenges and opportunities for cybersecurity software vendors. Consumer behavior shifts towards increased awareness of data security and privacy have fueled demand for robust security solutions. The forecast period (2025-2033) projects continued growth, with a projected CAGR of xx% driven by factors such as increasing adoption of cloud security, the rise of AI and machine learning in cybersecurity, and the growing adoption of IoT devices. Market penetration is expected to reach xx% by 2033.
Dominant Regions, Countries, or Segments in Cybersecurity Software Industry
North America currently leads the cybersecurity software industry in terms of market share. This dominance is attributed to its advanced technological infrastructure, well-established and stringent regulatory frameworks, and a deep pool of highly skilled cybersecurity professionals. However, the Asia-Pacific region is poised for the highest growth rate in the coming years. This accelerated expansion is driven by rapid digitalization across various industries, significant government investments in bolstering national cybersecurity capabilities, and a burgeoning awareness of cyber risks. Within market segmentation, cloud deployment models are experiencing rapid adoption due to their inherent scalability, flexibility, and cost-effectiveness, making them attractive for businesses of all sizes. Concurrently, the Software segment continues to dominate in terms of overall revenue share, owing to its pervasive application across diverse security needs. The BFSI, Healthcare, and Government & Defense sectors remain the principal end-user segments, driven by their critical need for robust data security and unwavering adherence to complex compliance mandates.
- North America: Holds the largest market share, propelled by mature technology adoption, robust regulatory enforcement, and a well-developed cybersecurity ecosystem.
- Asia-Pacific: Exhibits the highest projected growth potential, fueled by rapid digital transformation initiatives and substantial government investments in national cybersecurity infrastructure.
- Cloud Deployment: Stands out as the fastest-growing deployment model, offering organizations unparalleled scalability, agility, and cost efficiencies in managing their security posture.
- Software Offering: Remains the largest revenue contributor, reflecting the fundamental role of specialized software in addressing a broad spectrum of cybersecurity challenges.
- BFSI, Healthcare, Government & Defense: These sectors are the largest end-users, their critical reliance on data security and adherence to stringent compliance requirements making them primary consumers of advanced cybersecurity solutions.
Cybersecurity Software Industry Product Landscape
The cybersecurity software market is characterized by a comprehensive and continually expanding product portfolio designed to address a vast array of digital threats. This landscape includes essential solutions such as endpoint protection platforms (EPP) and endpoint detection and response (EDR) for safeguarding individual devices, robust network security solutions for monitoring and controlling traffic, and sophisticated cloud security platforms to protect data and applications hosted in cloud environments. Further critical offerings include data loss prevention (DLP) systems to prevent unauthorized data exfiltration and security information and event management (SIEM) solutions for centralized logging, analysis, and threat correlation. Recent innovations are heavily focused on leveraging AI for predictive threat detection, implementing automated security response mechanisms to mitigate threats in real-time, and ensuring seamless integration with cloud-native architectures. Key product differentiators in this competitive market revolve around user-friendliness, the efficacy and speed of threat detection, and the scalability of solutions across diverse IT infrastructures and platforms. Continuous technological advancements are driving the development of increasingly sophisticated and adaptive security solutions capable of effectively countering the evolving complexity and sophistication of modern cyber threats.
Key Drivers, Barriers & Challenges in Cybersecurity Software Industry
Key Drivers:
- The unrelenting increase in the frequency, sophistication, and impact of cyberattacks and data breaches across all industries.
- The accelerated adoption of cloud computing services and the proliferation of interconnected Internet of Things (IoT) devices, expanding the attack surface.
- The growing imperative of adhering to stringent government regulations and industry-specific compliance requirements related to data protection and privacy.
- A heightened global awareness among businesses and individuals regarding the importance of data privacy and cybersecurity, driving proactive security investments.
Key Challenges and Restraints:
- The significant initial cost of implementing and the ongoing expense of maintaining comprehensive cybersecurity solutions, posing a barrier for some organizations.
- A persistent and critical shortage of skilled cybersecurity professionals, hindering organizations' ability to effectively deploy, manage, and respond to threats.
- The inherent complexity of managing and securing increasingly diverse and distributed IT environments, including on-premises, cloud, and hybrid infrastructures.
- The dynamic and ever-evolving nature of cyber threats, requiring continuous adaptation and innovation in security technologies and strategies.
- Vulnerabilities within global supply chains, impacting the availability and integrity of crucial hardware and software components, leading to an estimated annual loss of approximately $250 million in disruptions and compromised systems.
Emerging Opportunities in Cybersecurity Software Industry
- Growing demand for security solutions for IoT devices and 5G networks.
- Increased adoption of AI and machine learning in cybersecurity.
- Expansion into untapped markets in developing economies.
- Development of innovative security solutions for the cloud and edge computing.
Growth Accelerators in the Cybersecurity Software Industry
The cybersecurity software industry is poised for sustained growth, driven by technological advancements, strategic partnerships, and increasing market penetration in emerging economies. The integration of AI and machine learning is enhancing threat detection and response capabilities. Strategic partnerships between cybersecurity vendors and cloud providers are expanding the reach and capabilities of security solutions. Expansion into untapped markets in developing economies presents significant growth opportunities.
Key Players Shaping the Cybersecurity Software Market
- Check Point Software Technologies
- IBM Corporation
- Sophos Ltd
- Zscaler Inc
- Fortinet Inc
- F5 Networks Inc
- Cisco Systems Inc
- Broadcom Inc
- Microsoft Corporation
- Proofpoint Inc
- Mandiant Inc
- CyberArk Software Ltd
- Palo Alto Networks Inc
Notable Milestones in Cybersecurity Software Industry Sector
- March 2022: Google Cloud's strategic acquisition of Mandiant for USD 5.4 billion underscored the market's recognition of the critical value and growing demand for proactive, intelligence-driven cybersecurity solutions and incident response capabilities.
- April 2022: Comcast Business's significant expansion of its partnership with Cisco Systems aimed to bolster integrated security offerings, particularly in the burgeoning market for Software-Defined Wide Area Network (SD-WAN) security solutions, enhancing secure connectivity for businesses.
In-Depth Cybersecurity Software Industry Market Outlook
The future of the cybersecurity software market is bright, driven by the relentless evolution of cyber threats and the increasing reliance on digital technologies. Strategic partnerships, technological innovation, and expanding market penetration in emerging economies will be key drivers of growth. The market is expected to witness continued consolidation through mergers and acquisitions, with an increased focus on AI-powered solutions and cloud security offerings. The market is projected to reach xx million units by 2033, presenting significant opportunities for both established players and new entrants.
Cybersecurity Software Industry Segmentation
-
1. Offering
- 1.1. Software
- 1.2. Services
-
2. Deployment
- 2.1. On-premises
- 2.2. Cloud
-
3. End User
- 3.1. BFSI
- 3.2. Healthcare
- 3.3. Manufacturing
- 3.4. Government & Defense
- 3.5. IT and Telecommunication
- 3.6. Other End Users
Cybersecurity Software Industry Segmentation By Geography
- 1. North America
- 2. Europe
- 3. Asia Pacific
- 4. Latin America
- 5. Middle East
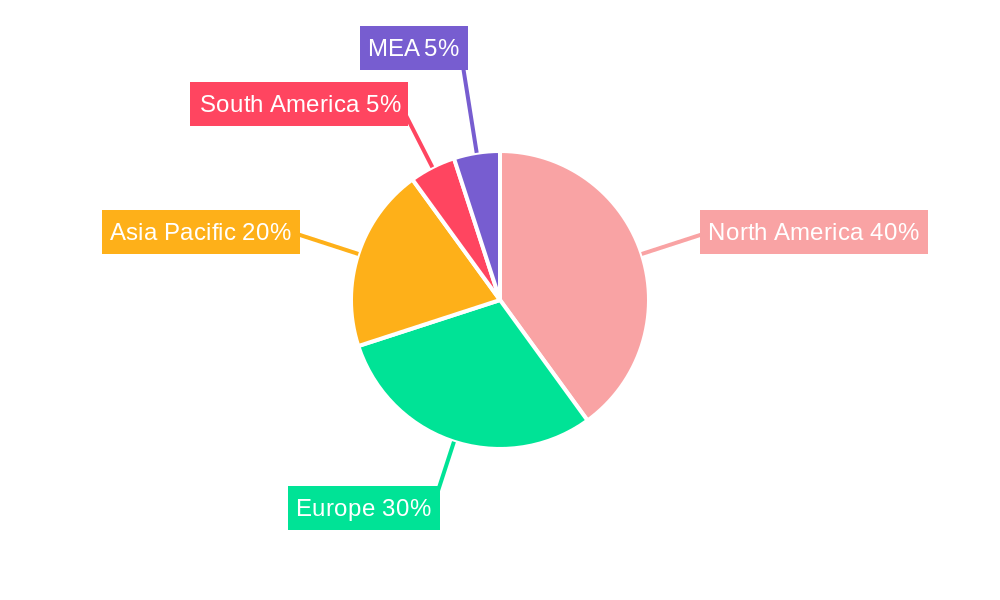
Cybersecurity Software Industry Regional Market Share

Geographic Coverage of Cybersecurity Software Industry
Cybersecurity Software Industry REPORT HIGHLIGHTS
| Aspects | Details |
|---|---|
| Study Period | 2020-2034 |
| Base Year | 2025 |
| Estimated Year | 2026 |
| Forecast Period | 2026-2034 |
| Historical Period | 2020-2025 |
| Growth Rate | CAGR of 11.9% from 2020-2034 |
| Segmentation |
|
Table of Contents
- 1. Introduction
- 1.1. Research Scope
- 1.2. Market Segmentation
- 1.3. Research Objective
- 1.4. Definitions and Assumptions
- 2. Executive Summary
- 2.1. Market Snapshot
- 3. Market Dynamics
- 3.1. Market Drivers
- 3.2. Market Restrains
- 3.3. Market Trends
- 3.4. Market Opportunities
- 4. Market Factor Analysis
- 4.1. Porters Five Forces
- 4.1.1. Bargaining Power of Suppliers
- 4.1.2. Bargaining Power of Buyers
- 4.1.3. Threat of New Entrants
- 4.1.4. Threat of Substitutes
- 4.1.5. Competitive Rivalry
- 4.2. PESTEL analysis
- 4.3. BCG Analysis
- 4.3.1. Stars (High Growth, High Market Share)
- 4.3.2. Cash Cows (Low Growth, High Market Share)
- 4.3.3. Question Mark (High Growth, Low Market Share)
- 4.3.4. Dogs (Low Growth, Low Market Share)
- 4.4. Ansoff Matrix Analysis
- 4.5. Supply Chain Analysis
- 4.6. Regulatory Landscape
- 4.7. Current Market Potential and Opportunity Assessment (TAM–SAM–SOM Framework)
- 4.8. IMR Analyst Note
- 4.1. Porters Five Forces
- 5. Market Analysis, Insights and Forecast 2021-2033
- 5.1. Market Analysis, Insights and Forecast - by Offering
- 5.1.1. Software
- 5.1.2. Services
- 5.2. Market Analysis, Insights and Forecast - by Deployment
- 5.2.1. On-premises
- 5.2.2. Cloud
- 5.3. Market Analysis, Insights and Forecast - by End User
- 5.3.1. BFSI
- 5.3.2. Healthcare
- 5.3.3. Manufacturing
- 5.3.4. Government & Defense
- 5.3.5. IT and Telecommunication
- 5.3.6. Other End Users
- 5.4. Market Analysis, Insights and Forecast - by Region
- 5.4.1. North America
- 5.4.2. Europe
- 5.4.3. Asia Pacific
- 5.4.4. Latin America
- 5.4.5. Middle East
- 5.1. Market Analysis, Insights and Forecast - by Offering
- 6. Global Cybersecurity Software Industry Analysis, Insights and Forecast, 2021-2033
- 6.1. Market Analysis, Insights and Forecast - by Offering
- 6.1.1. Software
- 6.1.2. Services
- 6.2. Market Analysis, Insights and Forecast - by Deployment
- 6.2.1. On-premises
- 6.2.2. Cloud
- 6.3. Market Analysis, Insights and Forecast - by End User
- 6.3.1. BFSI
- 6.3.2. Healthcare
- 6.3.3. Manufacturing
- 6.3.4. Government & Defense
- 6.3.5. IT and Telecommunication
- 6.3.6. Other End Users
- 6.1. Market Analysis, Insights and Forecast - by Offering
- 7. North America Cybersecurity Software Industry Analysis, Insights and Forecast, 2020-2032
- 7.1. Market Analysis, Insights and Forecast - by Offering
- 7.1.1. Software
- 7.1.2. Services
- 7.2. Market Analysis, Insights and Forecast - by Deployment
- 7.2.1. On-premises
- 7.2.2. Cloud
- 7.3. Market Analysis, Insights and Forecast - by End User
- 7.3.1. BFSI
- 7.3.2. Healthcare
- 7.3.3. Manufacturing
- 7.3.4. Government & Defense
- 7.3.5. IT and Telecommunication
- 7.3.6. Other End Users
- 7.1. Market Analysis, Insights and Forecast - by Offering
- 8. Europe Cybersecurity Software Industry Analysis, Insights and Forecast, 2020-2032
- 8.1. Market Analysis, Insights and Forecast - by Offering
- 8.1.1. Software
- 8.1.2. Services
- 8.2. Market Analysis, Insights and Forecast - by Deployment
- 8.2.1. On-premises
- 8.2.2. Cloud
- 8.3. Market Analysis, Insights and Forecast - by End User
- 8.3.1. BFSI
- 8.3.2. Healthcare
- 8.3.3. Manufacturing
- 8.3.4. Government & Defense
- 8.3.5. IT and Telecommunication
- 8.3.6. Other End Users
- 8.1. Market Analysis, Insights and Forecast - by Offering
- 9. Asia Pacific Cybersecurity Software Industry Analysis, Insights and Forecast, 2020-2032
- 9.1. Market Analysis, Insights and Forecast - by Offering
- 9.1.1. Software
- 9.1.2. Services
- 9.2. Market Analysis, Insights and Forecast - by Deployment
- 9.2.1. On-premises
- 9.2.2. Cloud
- 9.3. Market Analysis, Insights and Forecast - by End User
- 9.3.1. BFSI
- 9.3.2. Healthcare
- 9.3.3. Manufacturing
- 9.3.4. Government & Defense
- 9.3.5. IT and Telecommunication
- 9.3.6. Other End Users
- 9.1. Market Analysis, Insights and Forecast - by Offering
- 10. Latin America Cybersecurity Software Industry Analysis, Insights and Forecast, 2020-2032
- 10.1. Market Analysis, Insights and Forecast - by Offering
- 10.1.1. Software
- 10.1.2. Services
- 10.2. Market Analysis, Insights and Forecast - by Deployment
- 10.2.1. On-premises
- 10.2.2. Cloud
- 10.3. Market Analysis, Insights and Forecast - by End User
- 10.3.1. BFSI
- 10.3.2. Healthcare
- 10.3.3. Manufacturing
- 10.3.4. Government & Defense
- 10.3.5. IT and Telecommunication
- 10.3.6. Other End Users
- 10.1. Market Analysis, Insights and Forecast - by Offering
- 11. Middle East Cybersecurity Software Industry Analysis, Insights and Forecast, 2020-2032
- 11.1. Market Analysis, Insights and Forecast - by Offering
- 11.1.1. Software
- 11.1.2. Services
- 11.2. Market Analysis, Insights and Forecast - by Deployment
- 11.2.1. On-premises
- 11.2.2. Cloud
- 11.3. Market Analysis, Insights and Forecast - by End User
- 11.3.1. BFSI
- 11.3.2. Healthcare
- 11.3.3. Manufacturing
- 11.3.4. Government & Defense
- 11.3.5. IT and Telecommunication
- 11.3.6. Other End Users
- 11.1. Market Analysis, Insights and Forecast - by Offering
- 12. Competitive Analysis
- 12.1. Company Profiles
- 12.1.1 Check Point Software Technologies
- 12.1.1.1. Company Overview
- 12.1.1.2. Products
- 12.1.1.3. Company Financials
- 12.1.1.4. SWOT Analysis
- 12.1.2 IBM Corporation
- 12.1.2.1. Company Overview
- 12.1.2.2. Products
- 12.1.2.3. Company Financials
- 12.1.2.4. SWOT Analysis
- 12.1.3 Sophos Ltd *List Not Exhaustive
- 12.1.3.1. Company Overview
- 12.1.3.2. Products
- 12.1.3.3. Company Financials
- 12.1.3.4. SWOT Analysis
- 12.1.4 Zscaler Inc
- 12.1.4.1. Company Overview
- 12.1.4.2. Products
- 12.1.4.3. Company Financials
- 12.1.4.4. SWOT Analysis
- 12.1.5 Fortinet Inc
- 12.1.5.1. Company Overview
- 12.1.5.2. Products
- 12.1.5.3. Company Financials
- 12.1.5.4. SWOT Analysis
- 12.1.6 F5 Networks Inc
- 12.1.6.1. Company Overview
- 12.1.6.2. Products
- 12.1.6.3. Company Financials
- 12.1.6.4. SWOT Analysis
- 12.1.7 Cisco Systems Inc
- 12.1.7.1. Company Overview
- 12.1.7.2. Products
- 12.1.7.3. Company Financials
- 12.1.7.4. SWOT Analysis
- 12.1.8 Broadcom Inc
- 12.1.8.1. Company Overview
- 12.1.8.2. Products
- 12.1.8.3. Company Financials
- 12.1.8.4. SWOT Analysis
- 12.1.9 Microsoft Corporation
- 12.1.9.1. Company Overview
- 12.1.9.2. Products
- 12.1.9.3. Company Financials
- 12.1.9.4. SWOT Analysis
- 12.1.10 Proofpoint Inc
- 12.1.10.1. Company Overview
- 12.1.10.2. Products
- 12.1.10.3. Company Financials
- 12.1.10.4. SWOT Analysis
- 12.1.11 Mandiant Inc
- 12.1.11.1. Company Overview
- 12.1.11.2. Products
- 12.1.11.3. Company Financials
- 12.1.11.4. SWOT Analysis
- 12.1.12 CyberArk Software Ltd
- 12.1.12.1. Company Overview
- 12.1.12.2. Products
- 12.1.12.3. Company Financials
- 12.1.12.4. SWOT Analysis
- 12.1.13 Palo Alto Networks Inc
- 12.1.13.1. Company Overview
- 12.1.13.2. Products
- 12.1.13.3. Company Financials
- 12.1.13.4. SWOT Analysis
- 12.1.1 Check Point Software Technologies
- 12.2. Market Entropy
- 12.2.1 Company's Key Areas Served
- 12.2.2 Recent Developments
- 12.3. Company Market Share Analysis 2025
- 12.3.1 Top 5 Companies Market Share Analysis
- 12.3.2 Top 3 Companies Market Share Analysis
- 12.4. List of Potential Customers
- 13. Research Methodology
List of Figures
- Figure 1: Global Cybersecurity Software Industry Revenue Breakdown (undefined, %) by Region 2025 & 2033
- Figure 2: North America Cybersecurity Software Industry Revenue (undefined), by Offering 2025 & 2033
- Figure 3: North America Cybersecurity Software Industry Revenue Share (%), by Offering 2025 & 2033
- Figure 4: North America Cybersecurity Software Industry Revenue (undefined), by Deployment 2025 & 2033
- Figure 5: North America Cybersecurity Software Industry Revenue Share (%), by Deployment 2025 & 2033
- Figure 6: North America Cybersecurity Software Industry Revenue (undefined), by End User 2025 & 2033
- Figure 7: North America Cybersecurity Software Industry Revenue Share (%), by End User 2025 & 2033
- Figure 8: North America Cybersecurity Software Industry Revenue (undefined), by Country 2025 & 2033
- Figure 9: North America Cybersecurity Software Industry Revenue Share (%), by Country 2025 & 2033
- Figure 10: Europe Cybersecurity Software Industry Revenue (undefined), by Offering 2025 & 2033
- Figure 11: Europe Cybersecurity Software Industry Revenue Share (%), by Offering 2025 & 2033
- Figure 12: Europe Cybersecurity Software Industry Revenue (undefined), by Deployment 2025 & 2033
- Figure 13: Europe Cybersecurity Software Industry Revenue Share (%), by Deployment 2025 & 2033
- Figure 14: Europe Cybersecurity Software Industry Revenue (undefined), by End User 2025 & 2033
- Figure 15: Europe Cybersecurity Software Industry Revenue Share (%), by End User 2025 & 2033
- Figure 16: Europe Cybersecurity Software Industry Revenue (undefined), by Country 2025 & 2033
- Figure 17: Europe Cybersecurity Software Industry Revenue Share (%), by Country 2025 & 2033
- Figure 18: Asia Pacific Cybersecurity Software Industry Revenue (undefined), by Offering 2025 & 2033
- Figure 19: Asia Pacific Cybersecurity Software Industry Revenue Share (%), by Offering 2025 & 2033
- Figure 20: Asia Pacific Cybersecurity Software Industry Revenue (undefined), by Deployment 2025 & 2033
- Figure 21: Asia Pacific Cybersecurity Software Industry Revenue Share (%), by Deployment 2025 & 2033
- Figure 22: Asia Pacific Cybersecurity Software Industry Revenue (undefined), by End User 2025 & 2033
- Figure 23: Asia Pacific Cybersecurity Software Industry Revenue Share (%), by End User 2025 & 2033
- Figure 24: Asia Pacific Cybersecurity Software Industry Revenue (undefined), by Country 2025 & 2033
- Figure 25: Asia Pacific Cybersecurity Software Industry Revenue Share (%), by Country 2025 & 2033
- Figure 26: Latin America Cybersecurity Software Industry Revenue (undefined), by Offering 2025 & 2033
- Figure 27: Latin America Cybersecurity Software Industry Revenue Share (%), by Offering 2025 & 2033
- Figure 28: Latin America Cybersecurity Software Industry Revenue (undefined), by Deployment 2025 & 2033
- Figure 29: Latin America Cybersecurity Software Industry Revenue Share (%), by Deployment 2025 & 2033
- Figure 30: Latin America Cybersecurity Software Industry Revenue (undefined), by End User 2025 & 2033
- Figure 31: Latin America Cybersecurity Software Industry Revenue Share (%), by End User 2025 & 2033
- Figure 32: Latin America Cybersecurity Software Industry Revenue (undefined), by Country 2025 & 2033
- Figure 33: Latin America Cybersecurity Software Industry Revenue Share (%), by Country 2025 & 2033
- Figure 34: Middle East Cybersecurity Software Industry Revenue (undefined), by Offering 2025 & 2033
- Figure 35: Middle East Cybersecurity Software Industry Revenue Share (%), by Offering 2025 & 2033
- Figure 36: Middle East Cybersecurity Software Industry Revenue (undefined), by Deployment 2025 & 2033
- Figure 37: Middle East Cybersecurity Software Industry Revenue Share (%), by Deployment 2025 & 2033
- Figure 38: Middle East Cybersecurity Software Industry Revenue (undefined), by End User 2025 & 2033
- Figure 39: Middle East Cybersecurity Software Industry Revenue Share (%), by End User 2025 & 2033
- Figure 40: Middle East Cybersecurity Software Industry Revenue (undefined), by Country 2025 & 2033
- Figure 41: Middle East Cybersecurity Software Industry Revenue Share (%), by Country 2025 & 2033
List of Tables
- Table 1: Global Cybersecurity Software Industry Revenue undefined Forecast, by Offering 2020 & 2033
- Table 2: Global Cybersecurity Software Industry Revenue undefined Forecast, by Deployment 2020 & 2033
- Table 3: Global Cybersecurity Software Industry Revenue undefined Forecast, by End User 2020 & 2033
- Table 4: Global Cybersecurity Software Industry Revenue undefined Forecast, by Region 2020 & 2033
- Table 5: Global Cybersecurity Software Industry Revenue undefined Forecast, by Offering 2020 & 2033
- Table 6: Global Cybersecurity Software Industry Revenue undefined Forecast, by Deployment 2020 & 2033
- Table 7: Global Cybersecurity Software Industry Revenue undefined Forecast, by End User 2020 & 2033
- Table 8: Global Cybersecurity Software Industry Revenue undefined Forecast, by Country 2020 & 2033
- Table 9: Global Cybersecurity Software Industry Revenue undefined Forecast, by Offering 2020 & 2033
- Table 10: Global Cybersecurity Software Industry Revenue undefined Forecast, by Deployment 2020 & 2033
- Table 11: Global Cybersecurity Software Industry Revenue undefined Forecast, by End User 2020 & 2033
- Table 12: Global Cybersecurity Software Industry Revenue undefined Forecast, by Country 2020 & 2033
- Table 13: Global Cybersecurity Software Industry Revenue undefined Forecast, by Offering 2020 & 2033
- Table 14: Global Cybersecurity Software Industry Revenue undefined Forecast, by Deployment 2020 & 2033
- Table 15: Global Cybersecurity Software Industry Revenue undefined Forecast, by End User 2020 & 2033
- Table 16: Global Cybersecurity Software Industry Revenue undefined Forecast, by Country 2020 & 2033
- Table 17: Global Cybersecurity Software Industry Revenue undefined Forecast, by Offering 2020 & 2033
- Table 18: Global Cybersecurity Software Industry Revenue undefined Forecast, by Deployment 2020 & 2033
- Table 19: Global Cybersecurity Software Industry Revenue undefined Forecast, by End User 2020 & 2033
- Table 20: Global Cybersecurity Software Industry Revenue undefined Forecast, by Country 2020 & 2033
- Table 21: Global Cybersecurity Software Industry Revenue undefined Forecast, by Offering 2020 & 2033
- Table 22: Global Cybersecurity Software Industry Revenue undefined Forecast, by Deployment 2020 & 2033
- Table 23: Global Cybersecurity Software Industry Revenue undefined Forecast, by End User 2020 & 2033
- Table 24: Global Cybersecurity Software Industry Revenue undefined Forecast, by Country 2020 & 2033
Frequently Asked Questions
1. What is the projected Compound Annual Growth Rate (CAGR) of the Cybersecurity Software Industry?
The projected CAGR is approximately 11.9%.
2. Which companies are prominent players in the Cybersecurity Software Industry?
Key companies in the market include Check Point Software Technologies, IBM Corporation, Sophos Ltd *List Not Exhaustive, Zscaler Inc, Fortinet Inc, F5 Networks Inc, Cisco Systems Inc, Broadcom Inc, Microsoft Corporation, Proofpoint Inc, Mandiant Inc, CyberArk Software Ltd, Palo Alto Networks Inc.
3. What are the main segments of the Cybersecurity Software Industry?
The market segments include Offering, Deployment, End User.
4. Can you provide details about the market size?
The market size is estimated to be USD XXX N/A as of 2022.
5. What are some drivers contributing to market growth?
Increasing Demand for Digitalization and Scalable IT Infrastructure; Rapidly Increasing Cybersecurity Incidents and Regulations Requiring Their Reporting.
6. What are the notable trends driving market growth?
The BFSI End-User Segment is Expected to Witness Significant Growth.
7. Are there any restraints impacting market growth?
Computational Complexities.
8. Can you provide examples of recent developments in the market?
April 2022 - Comcast business announced the expansion of its strategic partnership with Cisco by adding Cisco SD-WAN powered by Viptela to its managed SD-WAN solution portfolio. The partnership expands the ability of the company to provide enterprise customers with comprehensive, global secure networking solutions with Ethernet, SD-WAN(software-defined vast area network), and security solutions.
9. What pricing options are available for accessing the report?
Pricing options include single-user, multi-user, and enterprise licenses priced at USD 4750, USD 5250, and USD 8750 respectively.
10. Is the market size provided in terms of value or volume?
The market size is provided in terms of value, measured in N/A.
11. Are there any specific market keywords associated with the report?
Yes, the market keyword associated with the report is "Cybersecurity Software Industry," which aids in identifying and referencing the specific market segment covered.
12. How do I determine which pricing option suits my needs best?
The pricing options vary based on user requirements and access needs. Individual users may opt for single-user licenses, while businesses requiring broader access may choose multi-user or enterprise licenses for cost-effective access to the report.
13. Are there any additional resources or data provided in the Cybersecurity Software Industry report?
While the report offers comprehensive insights, it's advisable to review the specific contents or supplementary materials provided to ascertain if additional resources or data are available.
14. How can I stay updated on further developments or reports in the Cybersecurity Software Industry?
To stay informed about further developments, trends, and reports in the Cybersecurity Software Industry, consider subscribing to industry newsletters, following relevant companies and organizations, or regularly checking reputable industry news sources and publications.
Methodology
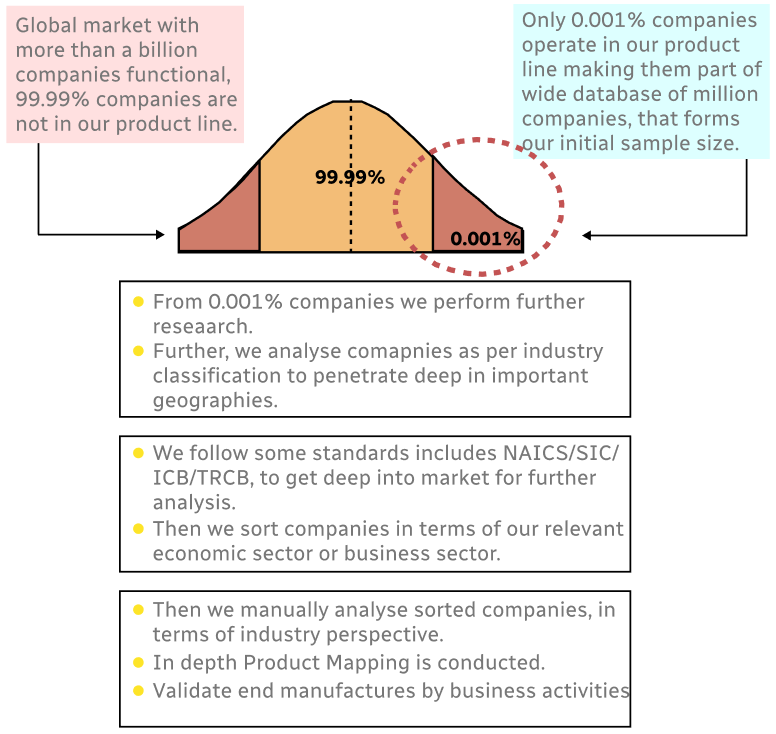
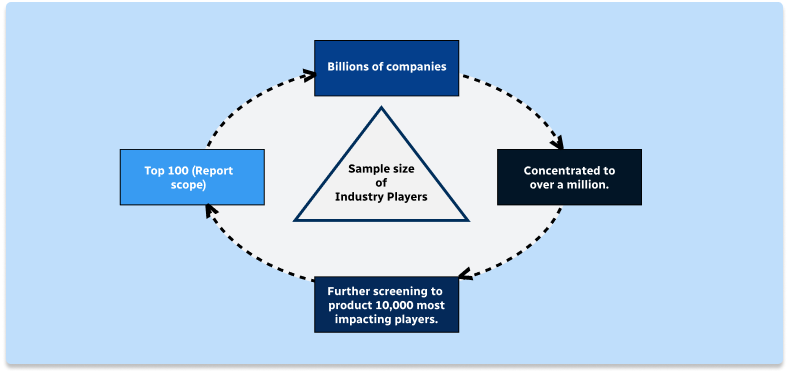
Step 1 - Identification of Relevant Samples Size from Population Database
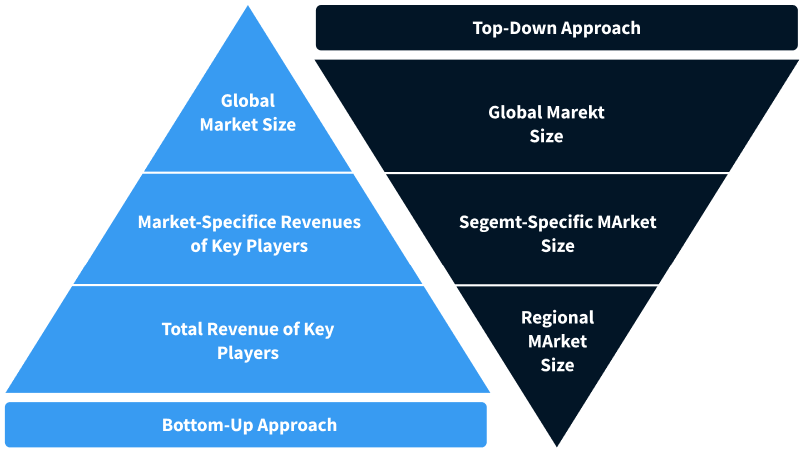
Step 2 - Approaches for Defining Global Market Size (Value, Volume* & Price*)
Note*: In applicable scenarios
Step 3 - Data Sources
Primary Research
- Web Analytics
- Survey Reports
- Research Institute
- Latest Research Reports
- Opinion Leaders
Secondary Research
- Annual Reports
- White Paper
- Latest Press Release
- Industry Association
- Paid Database
- Investor Presentations
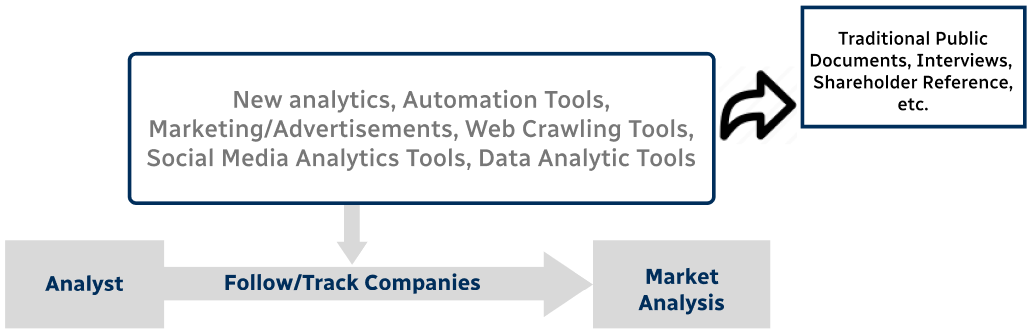
Step 4 - Data Triangulation
Involves using different sources of information in order to increase the validity of a study
These sources are likely to be stakeholders in a program - participants, other researchers, program staff, other community members, and so on.
Then we put all data in single framework & apply various statistical tools to find out the dynamic on the market.
During the analysis stage, feedback from the stakeholder groups would be compared to determine areas of agreement as well as areas of divergence


